Nettarsier Vulnerability Scan Tool
Nettarsier Vulnerability Scan Tool
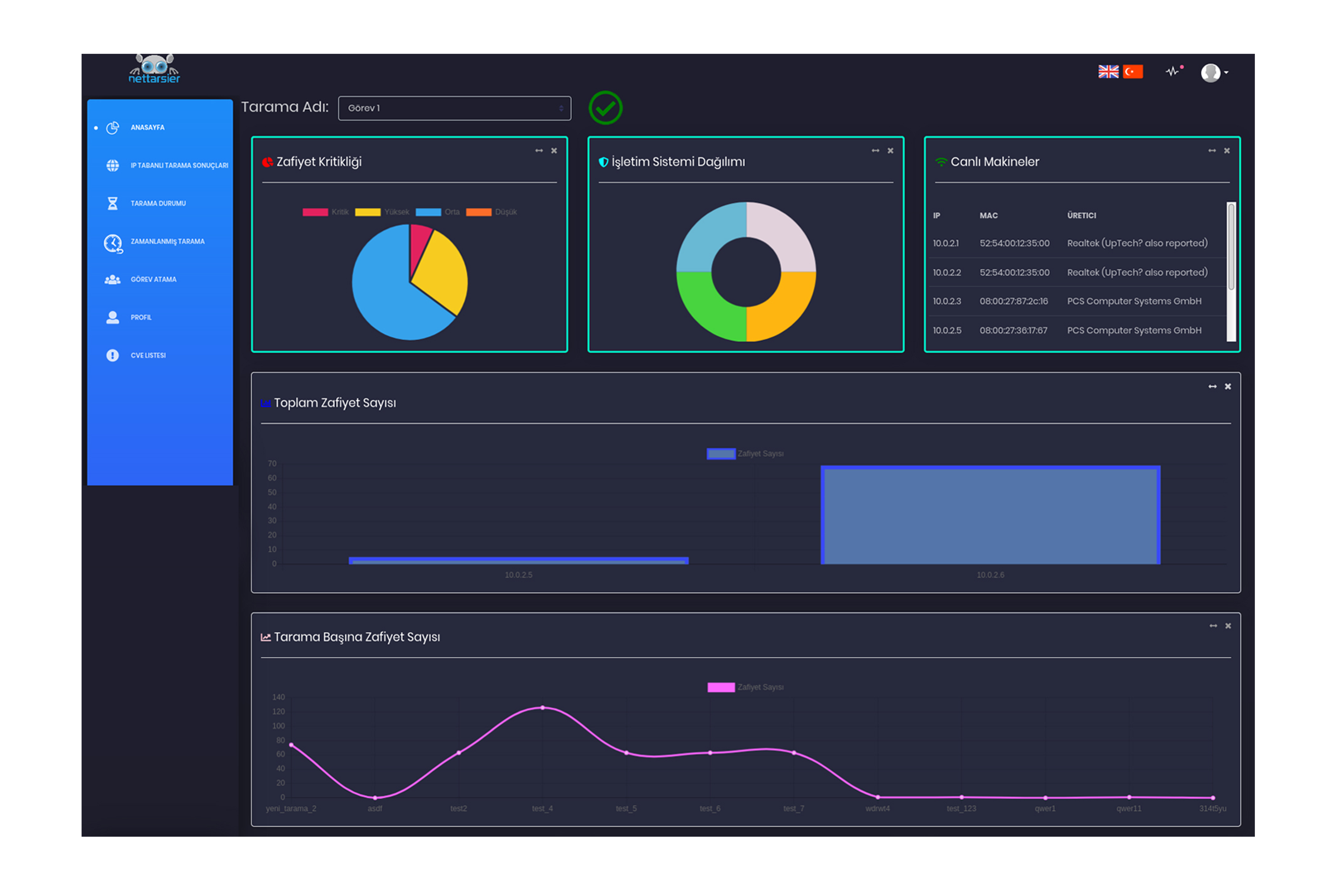
Nettarsier is a company that automatically scans the corporate network and services at desired periods, shows the detected vulnerabilities separately on a service basis and offers solutions for them, makes it possible to Assign Tasks regarding the vulnerabilities by the unit manager, presents all findings as a result report together with the executive summary. It is an extremely fast Enterprise Vulnerability Scanning Tool that can work integrated with other cyber security solutions, including SIEM.
Categories: Cyber Security
Tag: Cyber Attack, Vulnerability Scanning Tool
Features
- Language Option: It is possible to see the cyber security picture of the entire network in real time through the main panel screen that supports Turkish and English.
- Detailed Analysis: It also shows the vulnerabilities detected on that machine for the selected IP at the end of the scan in detail.
Blind Spot Access: It reflects a methodological approach to architectural penetration testing. It ensures that there are no blind spots in the scanning process. - High Speed: With its unique architecture, it completes scanning much faster than alternative vulnerability scanning tools.
- Automatic Scanning: It scans the target networks and systems periodically and automatically in specified time periods.
- Separate Option Presentation: It presents all critical findings separately on the main panel screen on a service-based basis.
- Solution Suggestions: It offers clear solution suggestions for the most common vulnerabilities detected.
- Offline Access: It can also work offline in the Corporate Closed Network environment without the Internet.
- Easy Installation: With its Docker infrastructure, it can be installed and managed independently of the operating system.
Technicial Specifications
- Access Protection: It closes easy entry points of systems by automatically trying predictable default user names and passwords on target services.
- Result Report: It presents a Final Report in HTML and PDF format, along with the Executive Summary of the issues identified in the scan results.
- Process Monitoring: It ensures that the detected vulnerabilities are assigned to the responsible person via the Task Assignment screen by the manager, the relevant person is informed via e-mail, and the process is followed.
- LOG Feed: It can provide log feed in json and syslog format via API library to SIEM and other security products operating in the Cyber Operations Center.
Please click for the brochure


